We are here today to talk about a very important topic: identity verification in a post-breach world.
Editor's note · Context
Discussing the significance of identity verification after data breaches.
Share & report
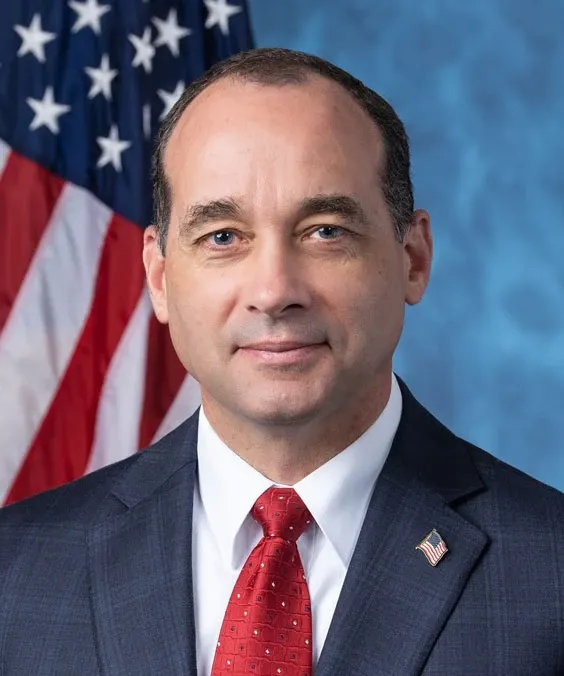
More from Howard Griffith
Mr. Speaker, the gentlewoman apologized for the noises on the floor. I love the noises and greatly appreciate having babies around. Mr. Speaker, I yield 4 minutes to the gentlewoman from North Carolina (Ms. Foxx).
Mr. Speaker, by direction of the Republican Conference, I offer a privileged resolution and ask for its immediate consideration. The Clerk read the resolution, as follows: H. Res. 107 Resolved, That the following named Member be, and is…
When debating this resolution, H.J. Res. 35, is it appropriate to discuss superfluous matters to the matter at hand currently on the floor? The SPEAKER pro tempore. Under clause 1 of rule XVII, remarks in debate must be confined to the…
Mr. Speaker, I yield myself the balance of my time to close. Mr. Speaker, I just have to say that I am appalled. I understand they get the right to say whatever they want to during this time of debate on the rule for the HALT Fentanyl Act…