On the recordOctober 22, 2015
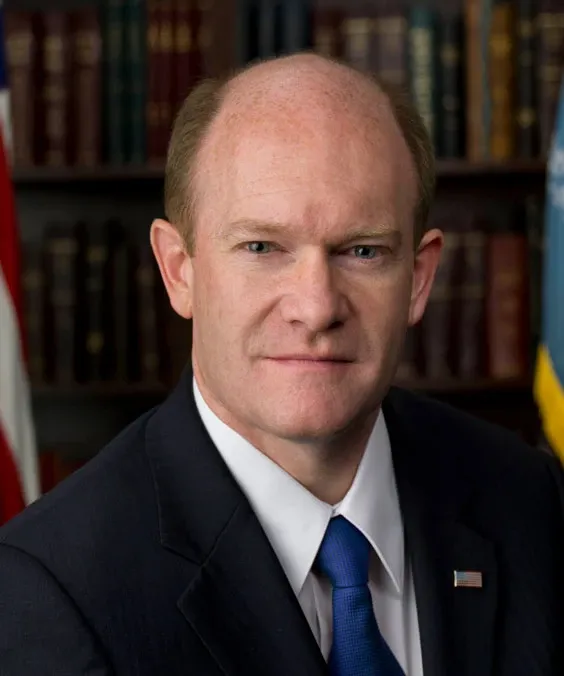
Colleagues, keep in mind, EINSTEIN 1 and EINSTEIN 2 are already effective to detect but not block these intrusions. EINSTEIN 3, authorized by our legislation, puts a new player on the field--a defensive player--to be able to block these intrusions. This is new and requires these agencies to implement that. For no other reason than that, it is a good reason to support this proposal. Thank you. The PRESIDING OFFICER. The Senator's time has expired. Cloture Motion The PRESIDING OFFICER. Pursuant to rule XXII, the Chair lays before the Senate the pending cloture motion, which the clerk will state. The legislative clerk read as follows: Cloture Motion We, the undersigned Senators, in accordance with the provisions of rule XXII of the Standing Rules of the Senate, do hereby move to bring to a close debate on amendment No. 2716 to S. 754, a bill to improve cybersecurity in the United States through enhanced sharing of information about cybersecurity threats, and for other purposes. Mitch McConnell, John Cornyn, Johnny Isakson, Richard Burr, John McCain, Shelley Moore Capito, Orrin G. Hatch, John Thune, Chuck Grassley, Pat Roberts, John Barrasso, Jeff Flake, Lamar Alexander, Bill Cassidy, Deb Fischer, Susan M. Collins, Patrick J. Toomey. The PRESIDING OFFICER. By unanimous consent, the mandatory quorum call has been waived. The question is, Is it the sense of the Senate that debate on amendment No. 2716, offered by the Senator from North Carolina, Mr. Burr, to S.…